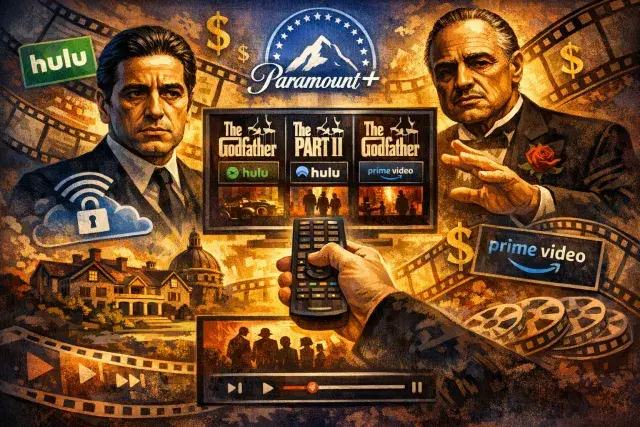
Millions of people across the United Kingdom have quietly made a significant shift in how they access the internet, turning to Virtual Private Networks in growing numbers to shield their activity from ISPs, advertisers, government agencies, and cybercriminals. The drivers are varied - intrusive age verification systems, rising awareness of data harvesting, and a broadening understanding that browsing without protection leaves a detailed trail that others can and do exploit. For many users, a VPN has become as routine as a password manager or antivirus software.
What a VPN Actually Does - and What It Cannot
A Virtual Private Network works by routing all internet traffic through an encrypted tunnel before it reaches its destination. The encryption scrambles your data into an unreadable sequence of characters, meaning your Internet Service Provider sees nothing identifiable about your browsing. Neither does your employer on a shared network, nor an advertiser attempting to build a behavioural profile from your activity. The VPN server acts as an intermediary, so websites and services register the server's IP address rather than your own - obscuring your physical location in the process.
This mechanism also eliminates a practice known as bandwidth throttling, where some ISPs deliberately slow connection speeds when they detect high-demand activity such as streaming or large file transfers. Because the VPN masks the nature of the traffic, the provider cannot make content-based decisions about your connection speed.
The limits are equally worth understanding. A VPN does not make you anonymous in every context. Logging into a Google account, social media platform, or any authenticated service restores the ability of that platform to track your behaviour - regardless of which server your traffic passes through. Payment processors retain the ability to link transactions to your identity. The protection a VPN offers is strongest against passive, infrastructure-level surveillance: your ISP, network administrators, and anyone intercepting unencrypted traffic on a public Wi-Fi connection.
Why ExpressVPN Has Become a Leading Choice for British Users
Among the providers competing for the British market, ExpressVPN has established a strong reputation built on independent verification rather than marketing claims alone. The service uses 256-bit Advanced Encryption Standard - the same protocol adopted by government and military agencies for securing classified information. The key space involved makes brute-force decryption with current computing technology effectively impossible.
Where ExpressVPN separates itself from many competitors is in the architecture of its server infrastructure. All servers operate on volatile RAM rather than conventional hard drives. Because RAM requires continuous power to retain data, every server reboot wipes all information completely. There is no persistent storage - meaning there is genuinely nothing to hand over if a legal request arrives.
That claim has been tested. KPMG has audited the company's no-logs policy on multiple occasions and confirmed it holds. PwC, Cure53, F-Secure, and Praetorian have each conducted independent security reviews covering everything from application integrity to privacy policy compliance. Independent auditing of this kind is the meaningful differentiator in a market where providers routinely make privacy promises that go unverified.
ExpressVPN is incorporated in the British Virgin Islands, a jurisdiction outside the Five Eyes intelligence-sharing agreement between the UK, US, Australia, Canada, and New Zealand. This matters because Five Eyes member states can compel domestic companies to hand over user data under national security provisions. Operating outside that framework, and under a legal system with no mandatory data retention requirements, means ExpressVPN faces no legal obligation to collect or preserve subscriber information in the first place.
What British Users Are Actually Getting for Their Subscription
Beyond the privacy architecture, ExpressVPN offers practical utility for everyday internet use. The service maintains servers in 105 countries, enabling access to geo-restricted content on platforms including BBC iPlayer, Sky Go, and international streaming libraries. Travellers and expatriates frequently use it to retain access to UK services from abroad - and vice versa, accessing international libraries unavailable in Britain.
A single subscription covers up to ten simultaneous device connections, spanning smartphones, tablets, laptops, smart TVs, and routers. The built-in kill switch - branded as Network Lock - automatically cuts internet access if the VPN connection drops unexpectedly, preventing unencrypted data from leaking through the gap. Split tunnelling allows users to route only selected applications through the VPN while letting other traffic use the standard connection, useful for those who want local network access alongside a private browsing session.
- Encryption standard: 256-bit AES, the protocol used by government and military agencies
- Server infrastructure: RAM-only, with all data wiped on every reboot
- Jurisdiction: British Virgin Islands, outside Five Eyes data-sharing agreements
- Independent audits: Conducted by KPMG, PwC, Cure53, F-Secure, and Praetorian
- Simultaneous connections: Up to ten devices per subscription
- Kill switch: Network Lock prevents data leaks if the VPN connection fails
- Money-back guarantee: 30 days, applicable to all subscription tiers
The pricing sits above budget alternatives, but the 30-day money-back guarantee removes the financial risk of testing the service. Longer-term subscriptions carry the most significant discounts, and for users whose primary concern is a documented, independently verified privacy infrastructure rather than the lowest possible price, the cost reflects what has been built and proven rather than simply promised.
The Broader Shift: Why Digital Privacy Has Become a Mainstream Concern
The growth in VPN adoption across Britain reflects something more substantial than a trend among technically inclined users. Awareness of commercial data harvesting has risen considerably since major platform data practices received sustained public and parliamentary scrutiny. The Online Safety Act and accompanying age verification requirements - which compel users to provide identifying information to access certain content - have prompted many people to think carefully about what data they are surrendering and to whom.
At the same time, public Wi-Fi networks remain as vulnerable as ever. Coffee shops, transport hubs, libraries, and university campuses all offer connections that, without a VPN, expose users to relatively straightforward interception techniques. The expansion of remote and hybrid working has added further motivation - employees handling sensitive files outside a managed office network face real exposure without some form of encrypted tunnel in place.
The decision to use a VPN has become less an enthusiast's choice and more a reasonable baseline precaution for anyone who would prefer that their browsing history, location, and online behaviour remain their own business. The technology is not a complete solution to digital privacy, but it addresses the most common and pervasive forms of surveillance that affect ordinary users every day.